uberAgent with Consist
When it comes to the analysis and security of application services, uberAgent is the perfect complement to Splunk. The uberAgent tool collects data at the endpoint and transfers it to Splunk.
User experience monitoring
uberAgent supplies information on all aspects of the user experience and application service at every Windows endpoint. Detailed inventory information shows which applications are used when, and how often, how reliable the application is, where problems exist with network connectivity, and much more.
The following screenshots show some of the most important features:

Logon duration
-> Is the user profile slow to load?
-> Has the logon script become too big?
-> Is the group policy being processed efficiently?
Endpoint security analytics
A data record on system activity as extensive as the one uberAgent generates is also highly relevant in terms of security. This is precisely why uberAgent ESA was developed. It prepares data specifically for security purposes.
uberAgent ESAG works purely in the area of applications and hardware, and monitors the technical parameters that occur during operation of the Windows client.
By hooking up to the client monitoring via Splunk, uberAgent ESA enables targeted monitoring of the data collected.
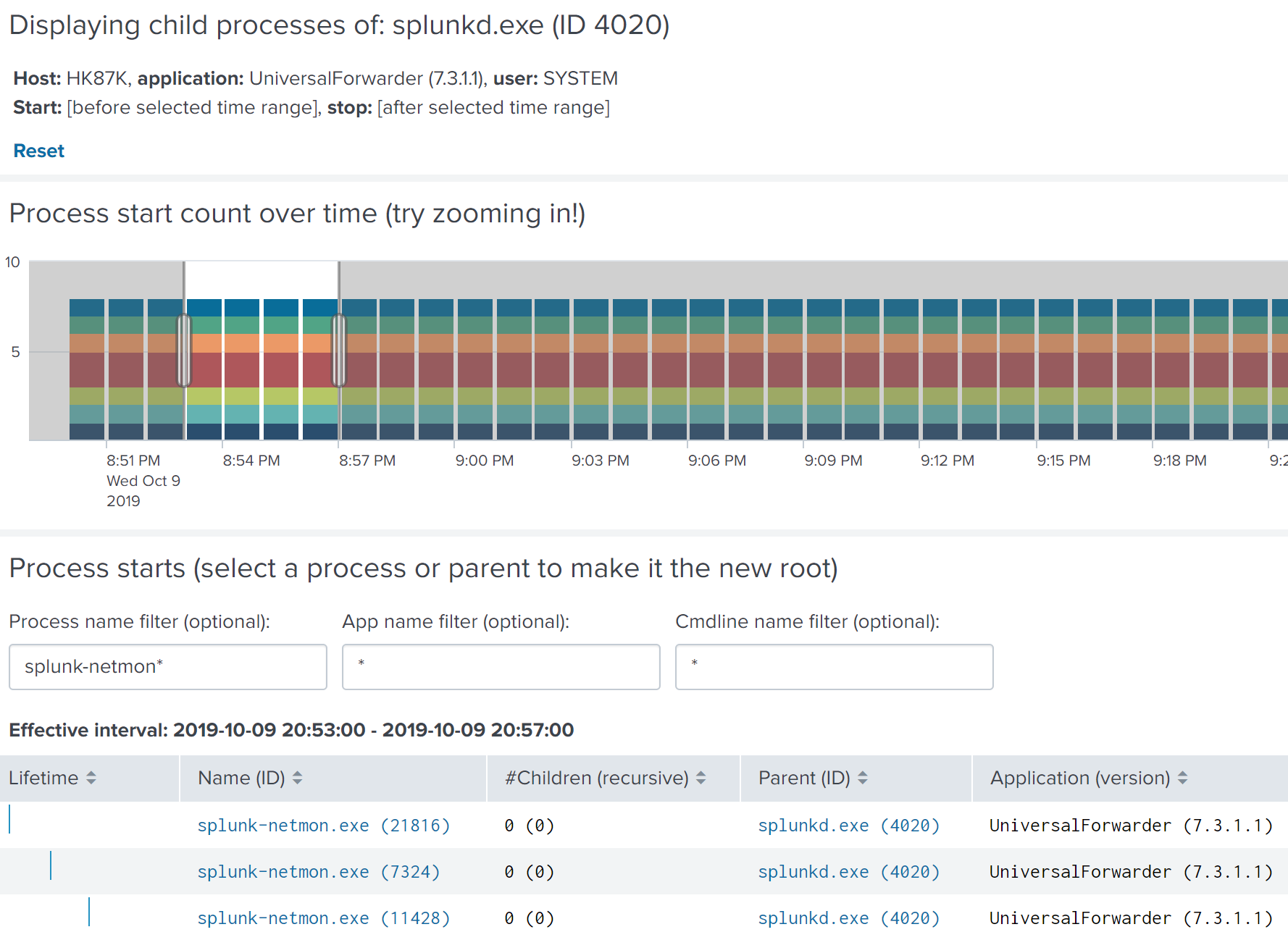
Process tree dashboard
The uberAgent ESA process tree dashboard enables simple navigation through complex hierarchies consisting of millions of parent-child process relationships and offers analysts a high-performance tool that allows them to make sense of process activities via interactive visualization.
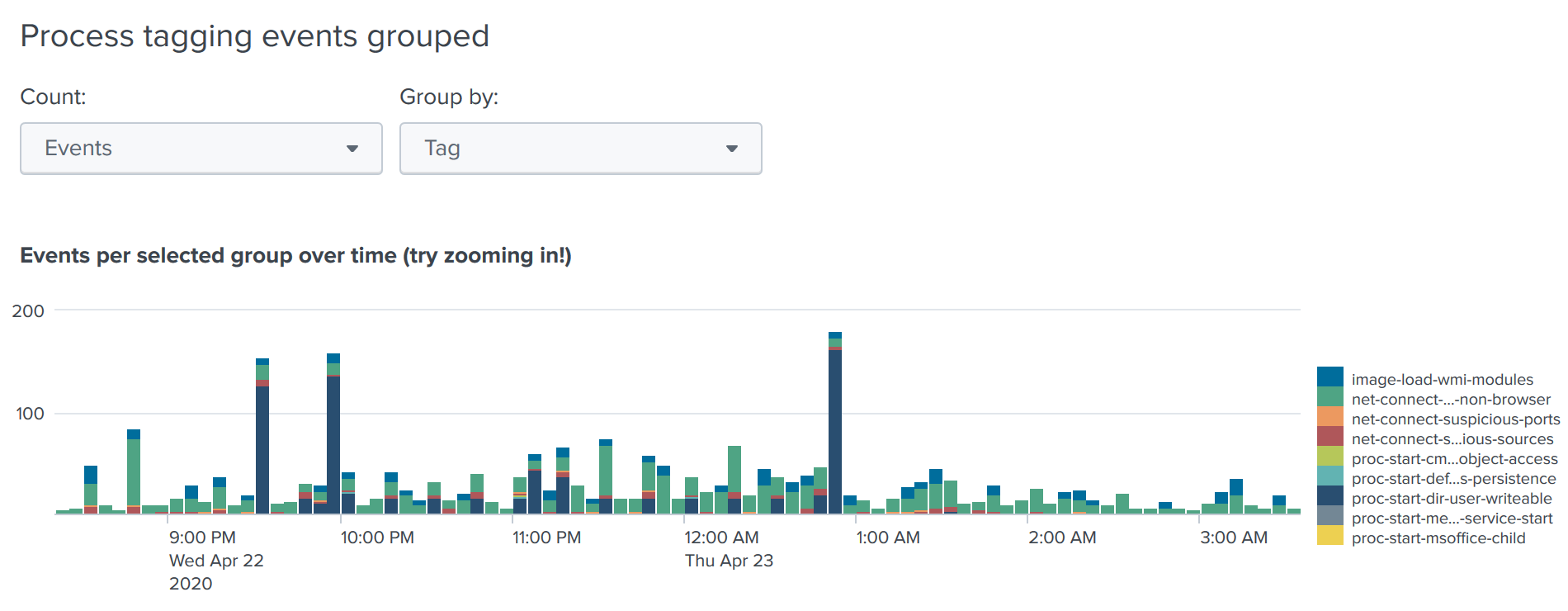
Tagging of event groups
A high-performance, flexible rule definition language enables companies to identify risky processes. Matching processes are given a tag and a risk assessment, both of which can be selected freely Process labeling rules can be organized in reusable blocks. All recognition elements support regular expressions and some even support a combination of regular expressions and environment variables.
uberAgent ESA contains predefined rules for many frequently occurring threats, including the identification of subordinate Microsoft Office processes. It is possible to label processes that are started by standard users of directories, in particular processes with low integrity that can be written to. Extended directory authorizations and SDDL analyses are also immediately available.
Your contact

Mirko Reich
Department Manager Sales & Marketing
phone: +49 431 3993-614
mobile: +49 173 4306503
e-mail: reich@consist.de